Our other sites:
In the UK, utilities refer to essential services that provide the basic infrastructure needed for everyday life and business operations. These services are typically provided by private companies or regulated entities and are crucial for public health, safety, and economic functioning. The primary utilities in the UK include energy, water and sewerage, telecommunications, waste management, and transport.
The UK’s utility sector faces growing demands as infrastructure ages and new investment projects are launched. According to Water UK, £96 billion is set to be invested in water and sewage infrastructure between 2025 and 2030 – a near-doubling of 2023 levels. Part of the proposal involves building ten new reservoirs to secure water supplies. Read more about reservoir security fencing in our dedicated blog post.
As these investments pour into modernising the UK's utility networks, it’s crucial for utility providers to implement robust perimeter security measures. These measures must evolve alongside the infrastructure upgrades, ensuring both cyber and physical security are integrated to effectively protect these high-value assets.
Why Perimeter Security is Critical for Utilities
Utilities in the UK are classified as Critical National Infrastructure (CNI), meaning they are essential for national security, public safety, and the economy. A security breach at a utility site can have far-reaching consequences, not just in terms of service availability, but also in the potential risks posed to public safety and national security. In light of these risks, perimeter security for utilities must go beyond simple fences and gates; it must form an integral part of a multi-layered, evolving security strategy.
The National Protective Security Authority (NPSA) emphasises the need for a holistic perimeter security solution; one that integrates fencing, gates, barriers, and surveillance systems while supporting operational processes. This should also account for how internal teams and external agencies, such as local law enforcement, will respond to incidents.
Developing a Security Plan for Utilities
The first step in creating an effective perimeter security plan for utilities is a detailed risk assessment to identify potential threats. This assessment should consider the Operational Requirements (OR) process, which evaluates the cost-benefit ratio and helps determine the most appropriate security measures for a given site. When specifying physical security measures such as fencing and gates, it’s critical to implement the 5 Ds of perimeter security:
1. Detect – Systems that identify intruders or suspicious activity as soon as it occurs.
2. Deter – Measures such as security fencing, fence spikes, and lighting that discourage potential intruders.
3. Delay – Fencing, road blockers, bollards and barriers that slow down vehicles, providing time for a response.
4. Deny – Secure fencing, with access control points that prevent entry, such as secure gates and access control systems.
5. Defend – The innermost ring of security, involving security personnel or police.
This layered approach is essential in not only defending assets but also enabling security teams to make informed, strategic responses.
Compliance with UK Regulations and Standards
To ensure perimeter security measures are effective and compliant, utilities must consider both legislative and operational requirements set out by regulatory bodies. These include:
National Protective Security Authority (NPSA): The NPSA provides guidelines on designing security measures that align with national security standards and practical site operations.
Health and Safety Executive (HSE): The HSE’s safety standards must be integrated with security measures to protect employees and contractors at utility sites.
Regulatory Bodies (Ofwat, Ofgem, etc.): Specific regulations apply to water, energy, and other utilities to ensure security compliance across sectors.
Perimeter security products, such as fencing, gates, and access control systems, must be carefully selected to meet these requirements. It’s crucial that these solutions are tested and certified by third parties to ensure they can withstand potential threats.
Security Product Standards and Accreditations
In the UK, perimeter security solutions for certain sectors such as CNI must be tested to meet specific standards. The most commonly required certification for perimeter security products is LPS 1175. This standard categorises products based on their ability to resist attack. The LPS 1175 rating system assesses products based on their ability to withstand various attack methods, including the use of power tools, and assigns them a security rating from A1 to H20. Products can be layered to achieve higher ratings.
Additionally, for sites that may be vulnerable to vehicle-based attacks, utilities should consider Hostile Vehicle Mitigation (HVM) measures. These include PAS 68 and IWA 14 certified barriers and gates, which are designed to prevent vehicles from breaching the perimeter, thus protecting both infrastructure and personnel.
Longevity and Cost Savings for Public, Government, and Customers
There is little value in developing security strategies, plans, and specifying products that meet the correct standards if those products are prone to rust, easily damaged, and not built to remain effective for the long term, such as 5 years or more. Durable, high-quality products with long guarantees like 25 years provide significant long-term financial and practical benefits and can save public or a utilities customers money. Here’s why longevity and product guarantees are important:
Enhancing Perimeter Security with Changing Trends and Technology
As the UK utility sector continues to modernise, integrating cutting-edge technology into perimeter security is becoming more common. Perimeter Intrusion Detection Systems (PIDS), along with advanced surveillance systems, including CCTV with AI-powered analytics, are essential for monitoring large and remote utility sites. These systems can detect intruders, assess threats in real-time, and reduce the need for physical patrols.
Furthermore, access control systems that use biometrics or RFID technology ensure that only authorised personnel are allowed access to sensitive areas. By combining physical barriers with smart technology, utilities can create an effective, comprehensive security strategy that’s both responsive and proactive.
Additionally, fencing styles are evolving, and it's important to consider how a standard security fence may not be very covert. Installing a traditional security fence around a high-security site can often draw attention, highlighting the area's vulnerability. However, there are now more discreet and aesthetically pleasing options that offer superior security features. These modern fences not only provide higher security ratings, better climb resistance, and noise reduction, but they also help minimise light pollution. Acoustic security barriers, for example, offer both effective protection and a more subtle appearance. Long-term guarantees, such as 25 years, are again essential to ensure these solutions remain effective.
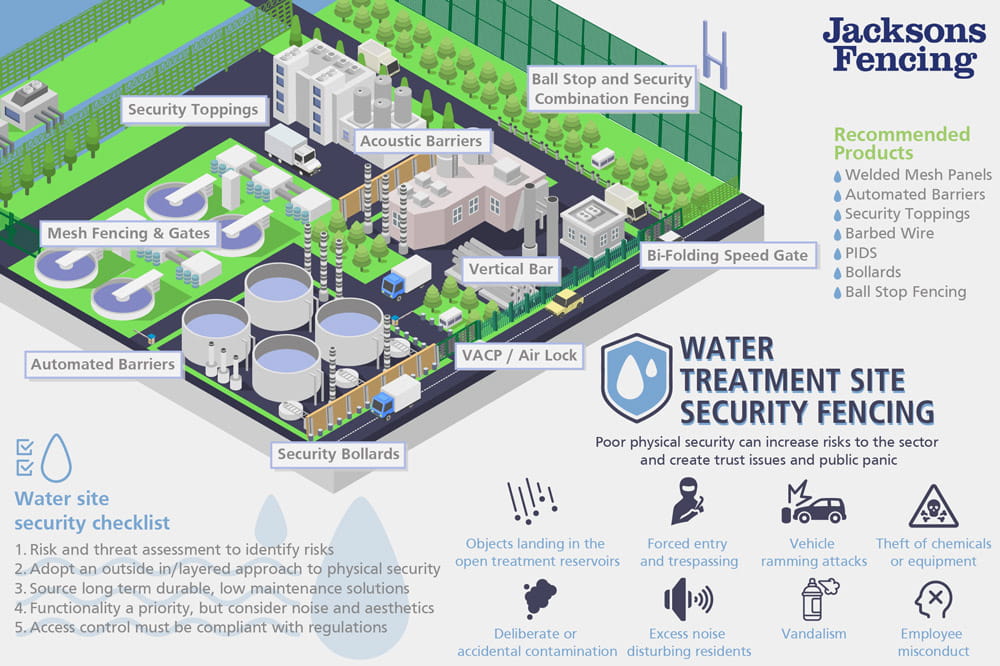
Real-World Application: Water Treatment Plant Case Study
To see how these advanced security measures are implemented in practice, look at how Jacksons Fencing upgraded the physical perimeter security for a water treatment plant. By installing security fencing, along with HVM and access control systems, the water treatment facility now has a robust security infrastructure that protects critical infrastructure while enabling easy monitoring and response.
As the UK’s utility sector continues to evolve and expand, perimeter security becomes an increasingly vital part of safeguarding critical infrastructure. By following the guidance of industry bodies like the NPSA and adhering to UK-specific regulations, utility providers can design and implement effective security solutions that address the full range of threats, whether physical, cyber, or hybrid. A layered approach that integrates physical deterrents with technology ensures that the UK’s utilities remain secure in the face of evolving risks.
If your utility company is looking to enhance its perimeter security, get in touch with Jacksons Fencing to explore the best practices and solutions for protecting your critical infrastructure.
Related products
Jacksons Security has a range of products relating to this article, all complete with our 25 year service life guarantee. If you cannot find the item you are looking for, please do not hesitate to call our friendly sales team.
Related Content
Top